|
It's not pretty in the bowels of the engine room. I refuse to play the game that our code is perfect. My code looks the same as what I look like on waking in the morning. It's a bit rough and needs a shave.
cheers
Chris Maunder
|
|
|
|
|
Simple: You post angry and abusive messages aimed at a long-standing member because two years ago he politely asked someone to use the correct forum for asking technical questions.
You then escalate by demanding the option to block users you don't like from seeing your comments.
Having drawn our attention to the thread[^], we all decide you're a troll, and you get kicked off the site. Et voila - no more CodeProject pixies forcing you to read and reply to old threads you don't like.
This is what's generally known as "the Streisand effect". Your messages had not been reported in the Spam & Abuse forum, and would probably have gone unnoticed if you hadn't drawn attention to them. By trying to be "clever" and drag the hamsters into your personal vendetta, you have only succeeded in harming yourself.
"These people looked deep within my soul and assigned me a number based on the order in which I joined."
- Homer
|
|
|
|
|
Richard Deeming wrote: This is what's generally known as "the Streisand effect".
As we say in Spain... Never go to bed without learning something new.
I didn't know that. Thanks  
M.D.V. 
If something has a solution... Why do we have to worry about?. If it has no solution... For what reason do we have to worry about?
Help me to understand what I'm saying, and I'll explain it better to you
Rating helpful answers is nice, but saying thanks can be even nicer.
|
|
|
|
|
Hello, I've just updated IntelliPort[^] article, but it is not shown on main site page! Is it intended? Thank you!
|
|
|
|
|
Because the update was minor it doesn't appear on the homepage.
cheers
Chris Maunder
|
|
|
|
|
The past couple of days has seen a flood of new spambot accounts. Maybe the procedure for opening an account can be modified to attenuate this. If not, I suspect the flood will continue, because it's easy for the spammers to keep pounding the site once they've automated it.
|
|
|
|
|
Something like
a.) Captcha
b.) Src IP check?
|
|
|
|
|
I dislike Captcha, and apparently so do the site hamsters, though it might be reasonable while creating and verifying an account.
Source IP address is even worse. Competent spammers use a VPN, which makes it impossible to distinguish them from legitimate users.
|
|
|
|
|
|
I'm no expert in this, so I didn't suggest a solution. If forced to answer, it'd be Captcha. 
|
|
|
|
|
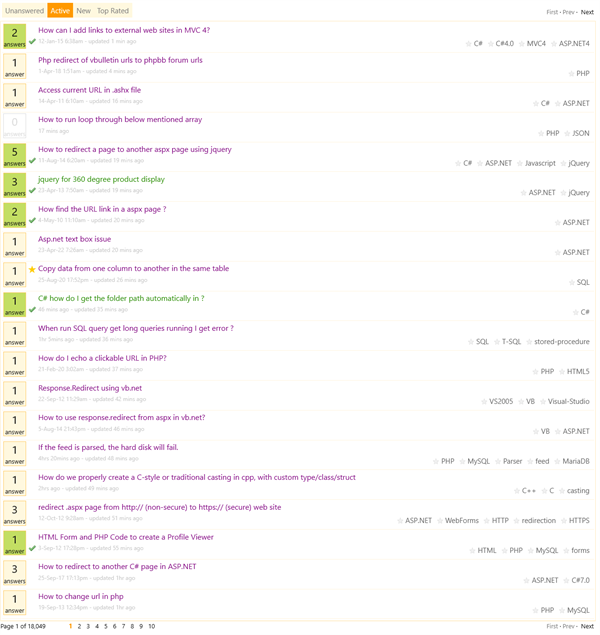
Every time I've looked at the first page of QA over the past couple of weeks, a certain set of questions posted between 2010 and 2018 are always at the top - seemingly all related to URLs and redirections.
For example, at the moment, on the first page of 20 questions, only six were posted within the last year:
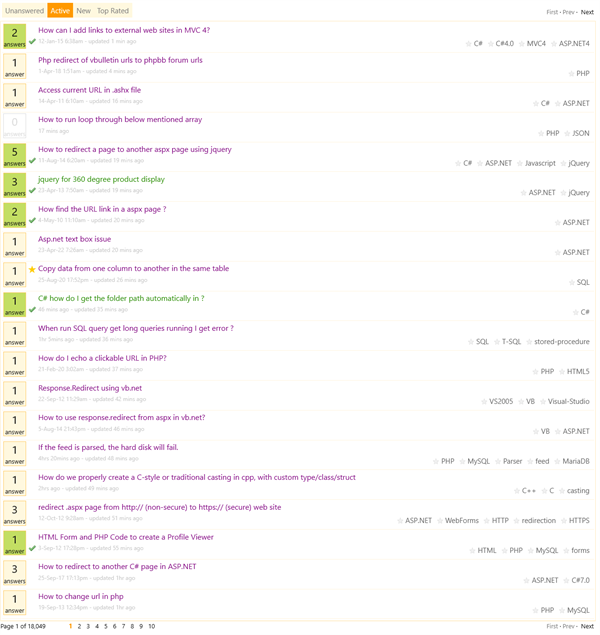
There's never any indication of what dragged them back to the top of the list. I suspect they're being actively targeted by a spam-bot, which isn't actually managing to get past the moderation filter.
If we can't have the questions drop back to their old position when a spam answer is deleted, and we can't prevent them from jumping to the top when a moderated spam answer is posted, is it perhaps worth "locking" these threads once they've been targeted multiple times?
"These people looked deep within my soul and assigned me a number based on the order in which I joined."
- Homer
|
|
|
|
|
Yep, we're seeing it too. I've added a task our end to help try and keep things sensible by resetting the "last active" date after spam has been removed.
cheers
Chris Maunder
|
|
|
|
|
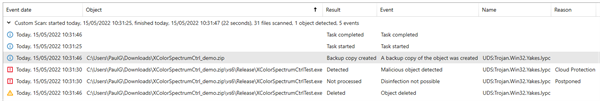
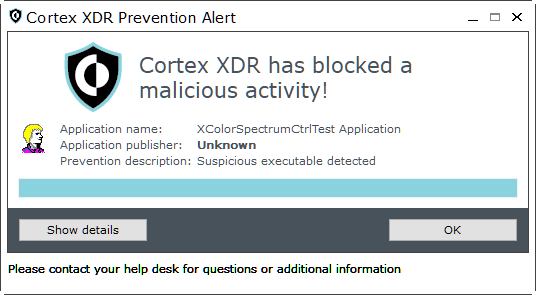
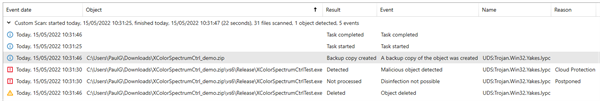
XColorSpectrumCtrl - a non-MFC color picker control that displays a color spectrum [^]
The download is flagged by Kaspersky (and possibly another AV) as containing a Trojan that wasn't detected until 3 years after the article was written = so it's probably a false positive, but can you look and remove the XColorSpecturmCtrlTest.EXE file from it?
"I have no idea what I did, but I'm taking full credit for it." - ThisOldTony
"Common sense is so rare these days, it should be classified as a super power" - Random T-shirt
AntiTwitter: @DalekDave is now a follower!
|
|
|
|
|
Sophos is also flagging it as infected.
|
|
|
|
|
May be legit detection then - but a trojan that escapes detection for three years but gets into a professional developer's EXE download? It's a bit too unlikely for my taste, but deleting the offending file is the best solution, just to be sure.
"I have no idea what I did, but I'm taking full credit for it." - ThisOldTony
"Common sense is so rare these days, it should be classified as a super power" - Random T-shirt
AntiTwitter: @DalekDave is now a follower!
|
|
|
|
|
Checked this again on another machine using Avast AV and it reckons its OK.
|
|
|
|
|
Paloalto Cortex XDR does let it through. Btw. XColorSpectrumCtrlTest.exe is dated on 2008.
|
|
|
|
|
And the trojan was detected in 2011 according to Kaspersky.
"I have no idea what I did, but I'm taking full credit for it." - ThisOldTony
"Common sense is so rare these days, it should be classified as a super power" - Random T-shirt
AntiTwitter: @DalekDave is now a follower!
|
|
|
|
|
Update:
Finally I try to run the app (and not only scan it by Cortex) and that is the result:
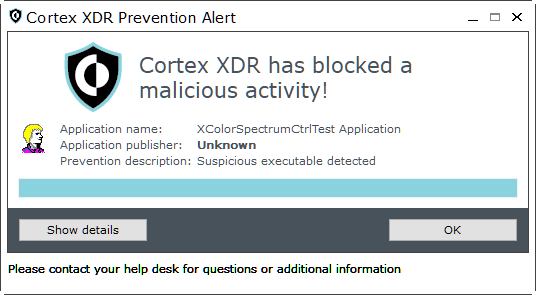
Application information:
Application name: XColorSpectrumCtrlTest Application
Application version: 1.1.0.1
Process ID: 3296
Application location: C:\Users\....\XColorSpectrumCtrlTest.exe
Command line: "C:\Users\....\XColorSpectrumCtrlTest.exe"
File origin: Hard drive on this computer
Prevention information:
Prevention date: Sonntag, 15. Mai 2022
Prevention time: 15:37:49
OS version: 10.0.19043.2.0.0.256.1
Component: WildFire
Cortex XDR code: c0400055
Prevention description: Suspicious executable detected
Additional information 1: C:\Users\....\XColorSpectrumCtrlTest.exe
Additional information 2: E6DA91998D5F224CC333A06D8E3EC59AB0F48501E16D5DCE696389D0B2C33C5C
Additional information 3: E6DA91998D5F224CC333A06D8E3EC59AB0F48501E16D5DCE696389D0B2C33C5C
Additional information 4:
[Edit]
I did not submit that until now to Paoloalto, maybe I will do it one time.
Anyway Cortex gives similar alarms with my own software when I do very low level access to USB devices.
I see it relaxed at the moment.
[Edit1]
After several logins to Paloalto they do not release it.... 
modified 15-May-22 11:28am.
|
|
|
|
|
All I can suggest, other than not using Kaspersky, is to submit it as a false positive to the anti-virus maker and wait. Their algorithms for matching malicious code are (understandably) weighted on false positives rather than false negatives.
cheers
Chris Maunder
|
|
|
|
|
Quote: I am trying to download the source code of this article in your site "XML File to SQL Database
XML File to SQL Database[^]
I got an error message can anyone help me in this
Quote: This is what I got when I CLICK download:
Ticket:
Error: An error occurred in this page. The error has been recorded and the site administrator informed.
Abort, Retry, Fail?_
|
|
|
|
|
On the article webpage click on the "Browse Code" and find the .zip then right-click and "save-as". This should work. I think it worked for me at some point.
[EDIT]
Check that, the downloaded .zip is invalid ...
[/EDIT]
|
|
|
|
|
|
I added a tag to one of the questions so that it could easily be found. It resulted in a v4 version. But when I look at the changelog it attributes my edit to another member (The original poster).
Just wanted to mention it here in case it's a bug.
|
|
|
|
|
Which Question?
"Time flies like an arrow. Fruit flies like a banana."
|
|
|
|
 General
General  News
News  Suggestion
Suggestion  Question
Question  Bug
Bug  Answer
Answer  Joke
Joke  Praise
Praise  Rant
Rant  Admin
Admin